Android 17 operating system enhances privacy by introducing temporary location sharing and spyware protection systems, aiming to reduce harm from criminals and protect user data globally.
Google announced a major security upgrade for the Android 17 operating system, focusing on addressing issues widely affecting users, including scammers, ransomware, spyware, and device theft.
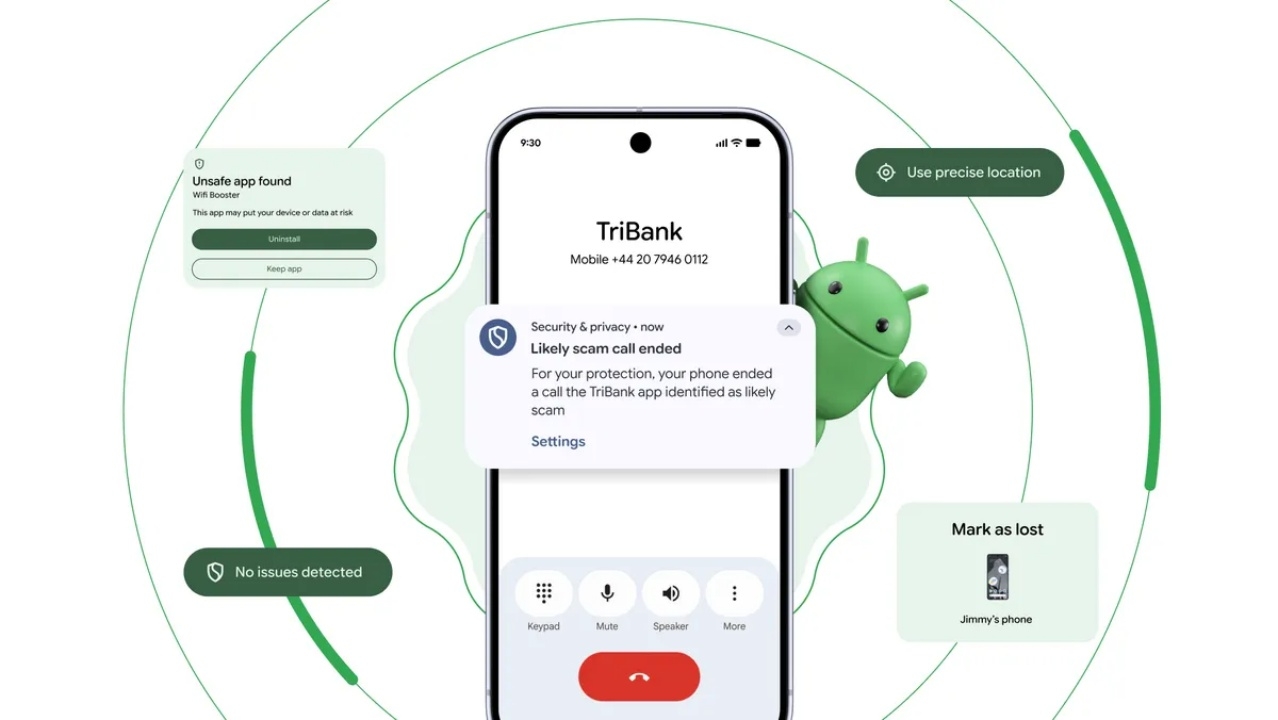
A key highlight is the system called Verified Financial Calls, which checks incoming calls against banking apps on the device in real time. If a call is identified as impersonation, the system automatically disconnects it to prevent huge annual losses caused by scammers. Additionally, banks can designate numbers as receive-only to block those numbers from being used for outgoing fraudulent calls.
Regarding malware monitoring, Google has strengthened the Live Threat Detection system by using AI to analyze suspicious app behaviors, such as secretly forwarding SMS messages or violating access to personal data.
Simultaneously, Google has added an Intrusion Logging feature for high-risk users like journalists and activists. This system records traces of digital attacks in encrypted logs for accurate investigation of hacking or spyware installation.
On theft protection, Android 17 introduces stronger anti-theft measures. The Mark as lost feature requires biometric authentication to access data, even if the thief knows the device's PIN or password. Once reported lost, the system blocks quick settings and disables new Wi-Fi and Bluetooth connections immediately to prevent thieves from evading tracking. It also introduces delay measures after repeated incorrect password attempts to prevent brute-force attacks.
For privacy control, Android 17 adds an option for temporary precise location sharing, allowing access to accurate location only while the app is in use. It also improves contact selection, enabling users to grant access only to specific contacts instead of the entire address book.
Furthermore, Google has added a system integrity verification feature to confirm the device runs standard software—not modified versions containing malware—along with hiding OTP codes from apps for up to three hours to reduce the risk of malware stealing verification codes for unauthorized transactions.